Blogs
Read our latest blog for insightful tips and knowledge!
Filter by

The Importance of SBOMs in Managing IoT Software Security
Building with open-source software is essential for many IoT developers. Open-source software provides a wealth…

The Human Factor in Container Security: Unlocking the Power of Awareness and Training
Containerization has revolutionized software development and deployment, allowing faster and more efficient application delivery. However,…

Why You Need To Take Advantage of The Free Trials For Container Security Management
Container security is one of the most important aspects of running a business today. With…
How Cloud Scanning Revolutionized Container Security
Cloud Scanning has become an essential component of any business' cybersecurity arsenal. Here's how it…
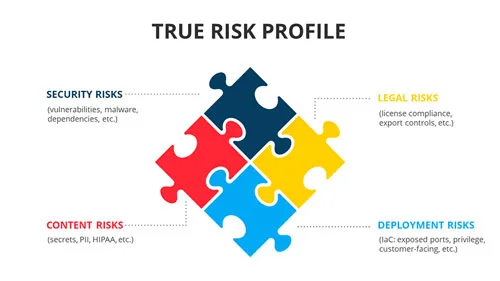
Container Security Asset Management
Container security is the practice of correlating all inherent security risks in conjunction with the…
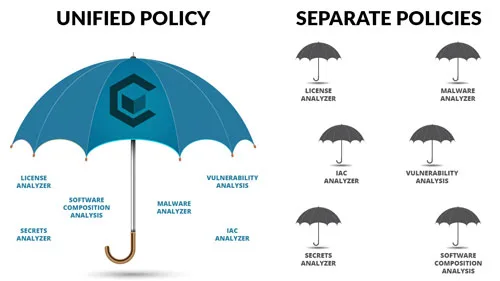
Choosing the Right Security Policy Solution
Security policies are a critical component of your security solution and selecting the right security…
Can AI Improve Code Security in DevOps? Exploring the Role of AI in Writing Secure Code
DevOps is a set of practices that combines software development and IT operations to enable…

Containerization and Microservices: The Future of DevOps
Technology advances and evolves, so do the approaches and methodologies in software development. One of…

Containerized Deployment Strategies for DevOps Teams
Containerization is changing the way that DevOps teams approach application deployment. By providing a portable,…

5 Ways to Improve Container Security in Your DevOps Pipeline
As DevOps has become a popular approach to software development, containerization has become an essential…
