Blogs
Read our latest blog for insightful tips and knowledge!
Filter by

The Human Factor in Container Security: Unlocking the Power of Awareness and Training
Containerization has revolutionized software development and deployment, allowing faster and more efficient application delivery. However,…
Docker vs. Kubernetes: What Are the Differences
When it comes to container orchestration, two powerful tools stand out: Docker and Kubernetes. Both…
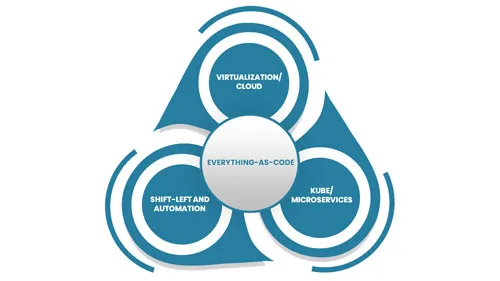
Everything-as-Code
Everything-as-Code (EaC) is the future of IT; the benefits are simply overwhelming. EaC is the…

Container Security: Comprehensive Analysis vs. Specialty Analyzers
Securing a container involves analyzing for a variety of potential risks over a variety of…
Human Errors in Container Security Incidents
Container security is crucial to keeping your containers safe and ensuring that your applications are…
6 Advantages of Open-Source Container Security
Open-source container security has many advantages over traditional security models. Let's look at some of…

4 Advantages of Cloud-Native Container Security
Cloud-native container security is a security model that focuses on protecting containers and the microservices…

Docker Registry: An Essential Tool for Container Image Management
Docker Registry is a critical component in the Docker ecosystem. It serves as a central…

Why Should You Leave Container Security in The Hands of Experts
Container security is a critical part of any organization's infrastructure and must be handled with…

The Advantages of Cloud-Native Security in Building Secure Applications
From computing down to data storage, cloud-native security is quickly becoming the preferred choice for…
