Blogs
Read our latest blog for insightful tips and knowledge!
Filter by
Why You Need Humans in Securing AI-Generated Code
Artificial intelligence (AI) is revolutionizing our world, and software development is no exception. AI-powered coding…
8 Ways Container Registry is Important and its Role in Cloud Native Development
As cloud-native development becomes more popular, the role of the container registry becomes more critical.…

How Container Security Platforms Help in the Aftermath of a Security Threat
In today's interconnected digital landscape, where security threats loom large, organizations continually seek robust solutions…
The Importance of Dependency Injection
Developers of the modern tech landscape are familiar with the concept of dependency injection and…
How Cloud Scanning Revolutionized Container Security
Cloud Scanning has become an essential component of any business' cybersecurity arsenal. Here's how it…

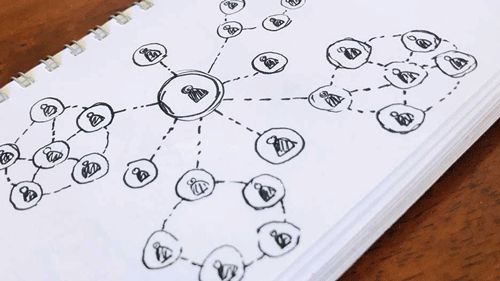
The Importance of SBOMs in Managing IoT Software Security
Building with open-source software is essential for many IoT developers. Open-source software provides a wealth…
The Challenges in Container Security That Can Be Overlooked
Container security is becoming increasingly important in the world of cloud computing. As containers become…
The Benefits of Network Functions Visualization
Software development teams, network operators and service providers all benefit from using Network Functions Visualization…
The Importance of Dependency Injection
Developers of the modern tech landscape are familiar with the concept of dependency injection and…

The Advantages of Containers Over Virtual Machines
Virtual machines changed the way IT departments delivered services, significantly increasing the speed and efficiency…
